The need for universal opt-in replay protection
SegWit2x got canceled, and with it probably the most heated "battle" in the Bitcoin space thus far draws to a close. There are many lessons to be learned from this ordeal as well as some other forks that are happening around Bitcoin - what constitutes "consensus" in the community, how will the future forks be handled and so on. One important aspect I haven't seen discussed as much currently is the ongoing issue of fork-proof replay protection - a feature that caused some controversy by its absence in SegWit2x and made Bitcoin Gold a laughing stock when they created a bounty for it very close to their forking date.
Crypto wallets remain at risk from phone hacks
With the prevalence of two-step authentication systems that use phone numbers to access email and virtual money accounts, phone hijacking is on the rise as a way to siphon funds from online cryptocurrency wallets.
The imperative for self-sovereign identification
I’m making a presentation on cybersecurity this week at our Nordic Finance Innovation meetings. This meant preparing a few new slides from scratch as I don’t have a set deck for cybercrime, and sat and started ideas just as the news dropped about the Equifax breach. You’ll all know about this by now, but over 143 million Equifax accounts were hacked during June-July 2017, including customers’ social security numbers, name, address, date of birth, driving licence and other sensitive info. In other words, all the information you need to open new accounts and access existing accounts.
Securing your free “Bitcoin Cash” stash
In the last days of July 2017, the Bitcoin miners have unanimously decided to signal for Segregated Witness, ending a years long scaling debate discussion. However a few participants decided to reject this decision and create their own Bitcoin fork, Bitcoin Cash (also known as BCC, ABC or UAHF). As a result, all Bitcoin holders will be granted a new duplicated Bitcoin Cash balance (literally airdropped free money) if the fork activates — this post and the follow ups will describe how you can best secure this new balance, then decide to trade it, hold it or sell it as you wish.
Fintech and Financial Services: Initial Considerations
A new wave of technological innovations, often called âfintech, â is accelerating change in the financial sector. What impact might fintech have on financial services, and how should regulation respond? This paper sets out an economic framework for thinking through the channels by which fintech might provide solutions that respond to consumer needs for trust, security, privacy, and better services, change the competitive landscape, and affect regulation. It combines a broad discussion of trends across financial services with a focus on cross-border payments and especially the impact of distributed ledger technology. Overall, the paper finds that boundaries among different types of service providers are blurring; barriers to entry are changing; and improvements in cross-border payments are likely. It argues that regulatory authorities need to balance carefully efficiency and stability trade-offs in the face of rapid changes, and ensure that trust is maintained in an evolving financial system. It also highlights the importance of international cooperation.
Letter to Loved Ones: a template for your cryptocurrency estate planning
Most people have never thought about what will happen to their bitcoin, ether, and other crypto-assets if something bad happens to them. Even if you do understand the concept of passing your crypto-assets to your loved ones, actually doing the work to make it happen is often a daunting prospect. It’s one of those tasks, without a hard deadline, that gets pushed to the end of your to-do list, repeatedly. Most people don’t know where to start and there are very few resources available to help guide you through the process. But it doesn’t have to be that way.
Antbleed exposes ‘70 percent’ of Bitcoin miners to attack
Antbleed.com recently revealed a backdoor in Bitmain’s Antminer series of Bitcoin miners, which allows attackers and Bitmain to remotely shut down the bitcoin mining hardware.
Tor May Use Bitcoin to Enable User-Friendly Onion Addresses
The Tor Project recently suggested that Blockstack may provide a solution to problems associated with onion addresses.
Accenture and Thales combine blockchain technology and hardware security modules
Global professional services firm Accenture PLC and Thales e-security recently announced the launch of a patent-pending security system for enterprise use that, “creates a simple path to large-scale commercial use of blockchain technology,” according to Accenture.
Bug Analyse Security Report On Blockchain Software
This security audit report of blockchain software by the National Computer Network Emergency Response Technical Team/Coordination Center of China (CNCERT) examines 25 open-source blockchain projects, categorizing the vulnerabilities found into 9 classes.
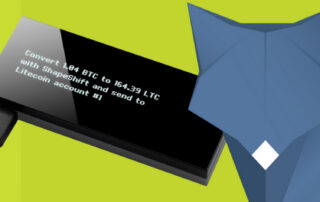
KeepKey and Shapeshift team up for dynamic and secure cryptocurrency trading
KeepKey and ShapeShift recently announced a partnership to create the first fully trustless, highly secure, process for trading cryptocurrencies. According to KeepKey, beta testing will begin next week.
Bitcoin security is more than multisig
Following the Bitfinex hack it’s become apparent that people don’t really understand bitcoin’s multisig feature. There seems to be a lot of confusion over what multisig is and isn’t, what it inherently does or does not do. This article aims to clarify some of the most common misconceptions, explain how multisig actually works today, why policy controls aren’t a substitute for organizational security, and what you can do to protect yourself.
Core Bitcoin developer claims ChainAnchor plans to bribe Bitcoin miners to regulate bitcoin
Peter Todd is one of the longest-serving core bitcoin developers remaining, a Canadian with 92 separate contributions to the bitcoin code base to date. He has worked on projects like Colored Coins, Counterparty, and Stealth Addresses, but is best known as someone who searches for vulnerabilities in the bitcoin system.
Gone Forever: Bitcoin, AltCoins, Asset‐Tokens, & Death
If you died tomorrow would your family inherit your bitcoin, altcoins, and asset-tokens? The answer depends on you. While legally, the answer is yes, if your passwords, passphrases, and key locations die with you that probably won’t happen. Without those things your crypto-assets will be inaccessible. Like gold coins buried in a meadow; they may know the treasure exists but they’ll never be able to access it.
HYPR brings biometrics to BitGo Bitcoin wallets
BitGo provides one of the most popular bitcoin wallets, having been integrated into exchanges and other bitcoin services including BitFinex, Bitstamp, Wirex (previously E-Coin), and Kraken.
Tech Trends 2016 – Innovating in the digital era
The 2016 report identifies eight trends that reflect macro forces fuelling innovation: digital, analytics, cloud, the renaissance of core systems, and the changing role of IT within the enterprise, balanced with the implications of cyber riskâsecurity, compliance, regulatory and compliance, quality, and safety.